Configure and Use the HashiCorp Vault KV Secret Engine
This doc provides steps to create and use a KV Secrets Engine on Vault to be used with Axual Platform.
These steps have been written with the governance secret engine as example,
this secret engine is required when using the Platform Manager with the Streaming charts, but
can be replaced with any other secret engine.
Initially, we need to initialize and unseal the HashiCorp Vault.
| Initialization is required once |
Initialize and Unseal the HashiCorp Vault
The first time you install the HashiCorp Vault, it requires to be initialized to have unseal key(s) and a root token.
More info can be found in the Vault official doc
-
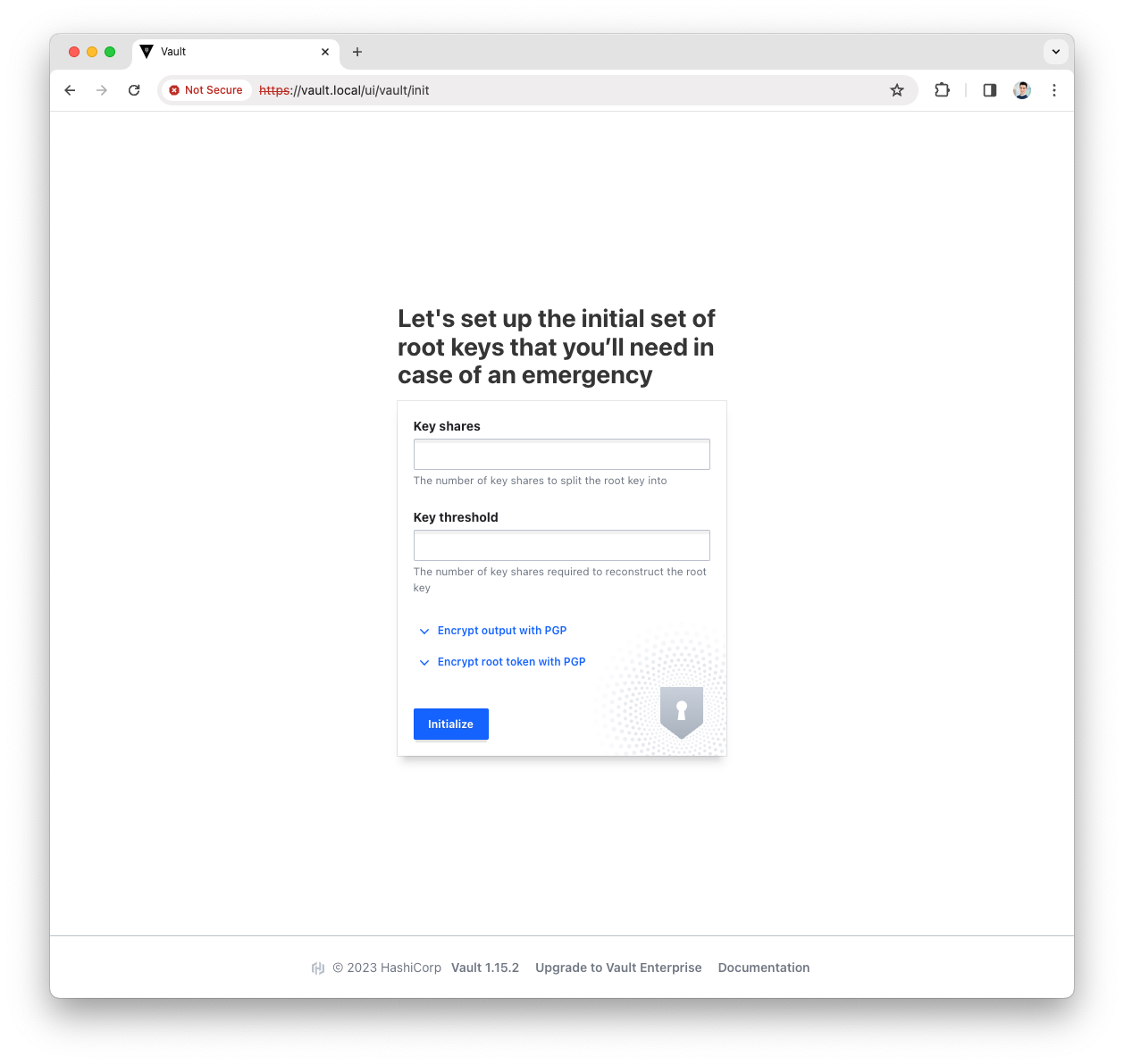
Access the Vault UI
-
Provide the
key sharesand thekey thresholdand pressInitializebuttonFor a production environment we suggest at least key_shares=3andkey_threshold=2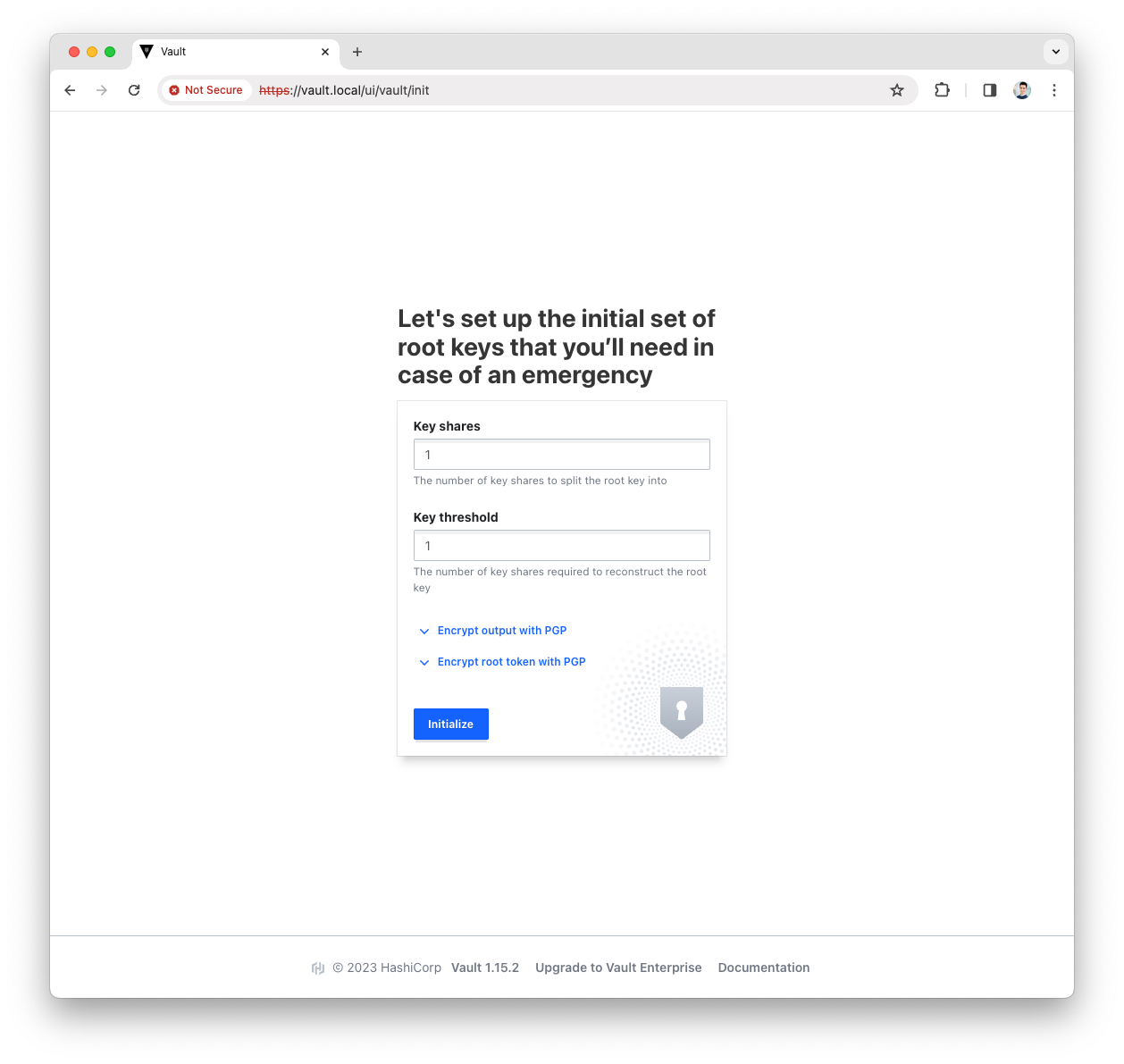
-
Download the generated keys
These will be used to unseal and access the Vault UI 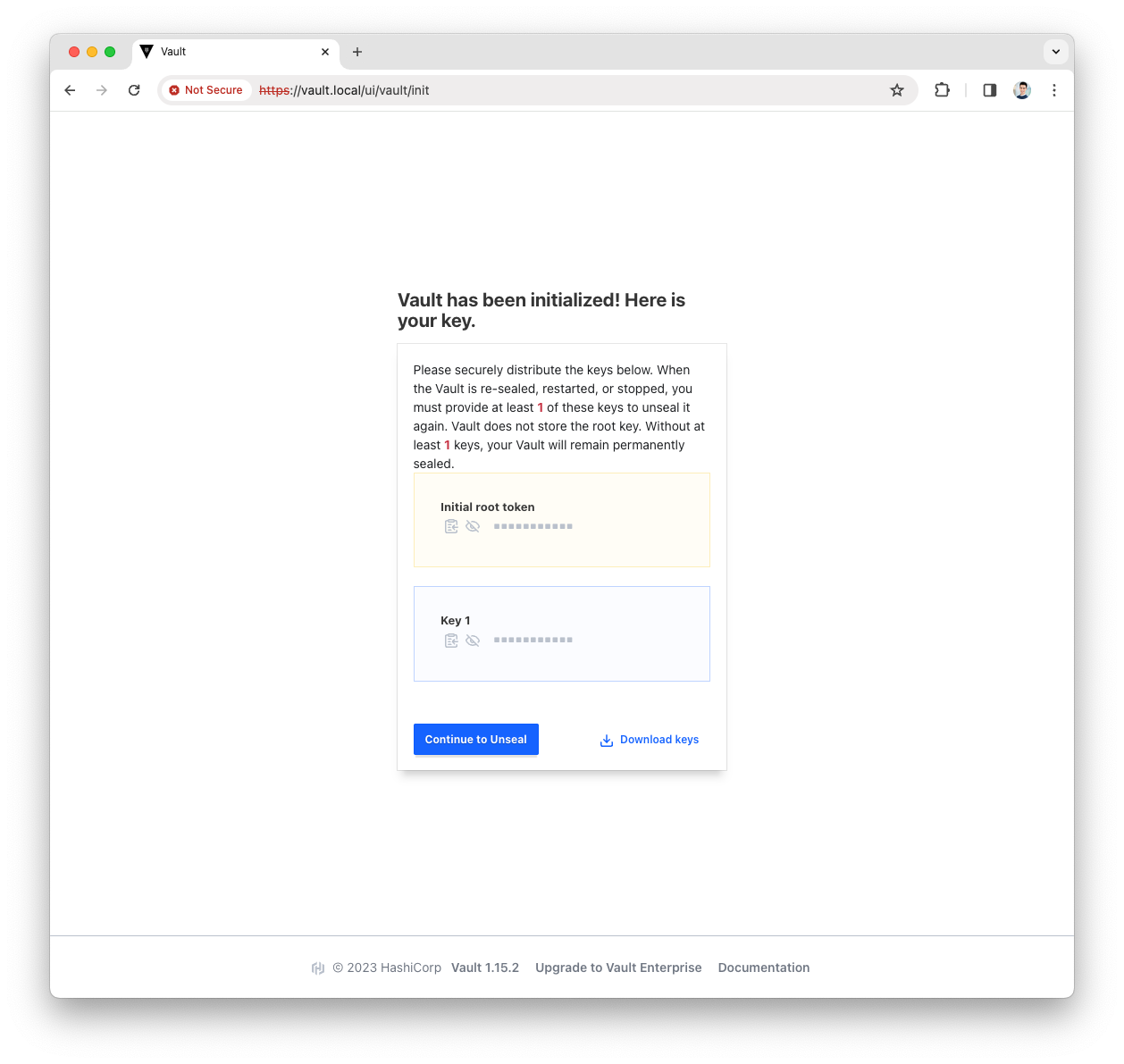
-
Press the
Continue to Unsealbutton -
Paste the Key(s) and press the
Unsealbutton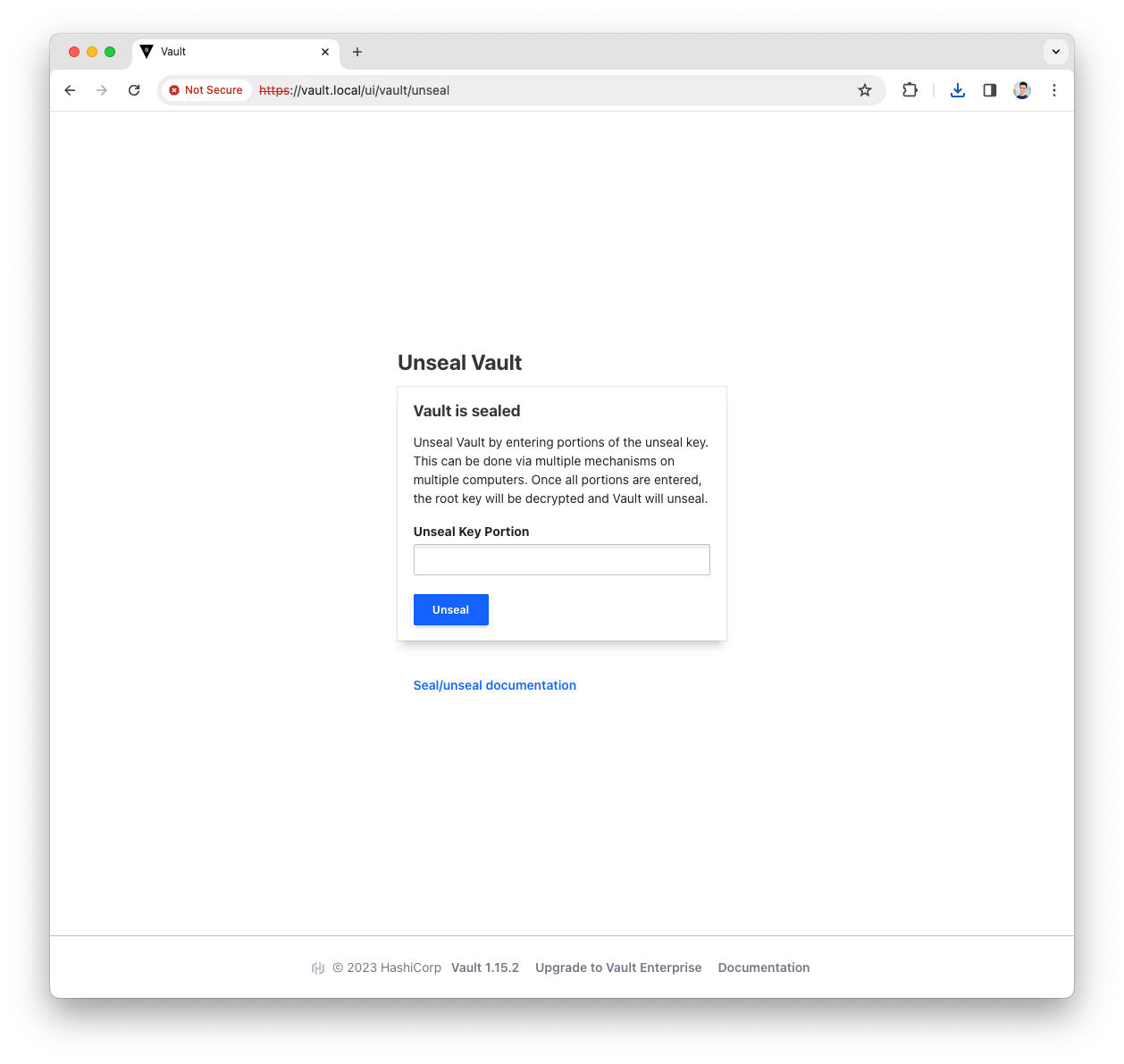
Based on the number of
key sharesandkey thresholdyou will have to repeat the above step with a different key.More info can be found in the Vault official doc
Enable the AppRole Auth Method
The AppRole auth method allows application to authenticate with Vault-defined roles.
More info can be found in the Vault official doc
-
Login into the Vault UI with your
rootToken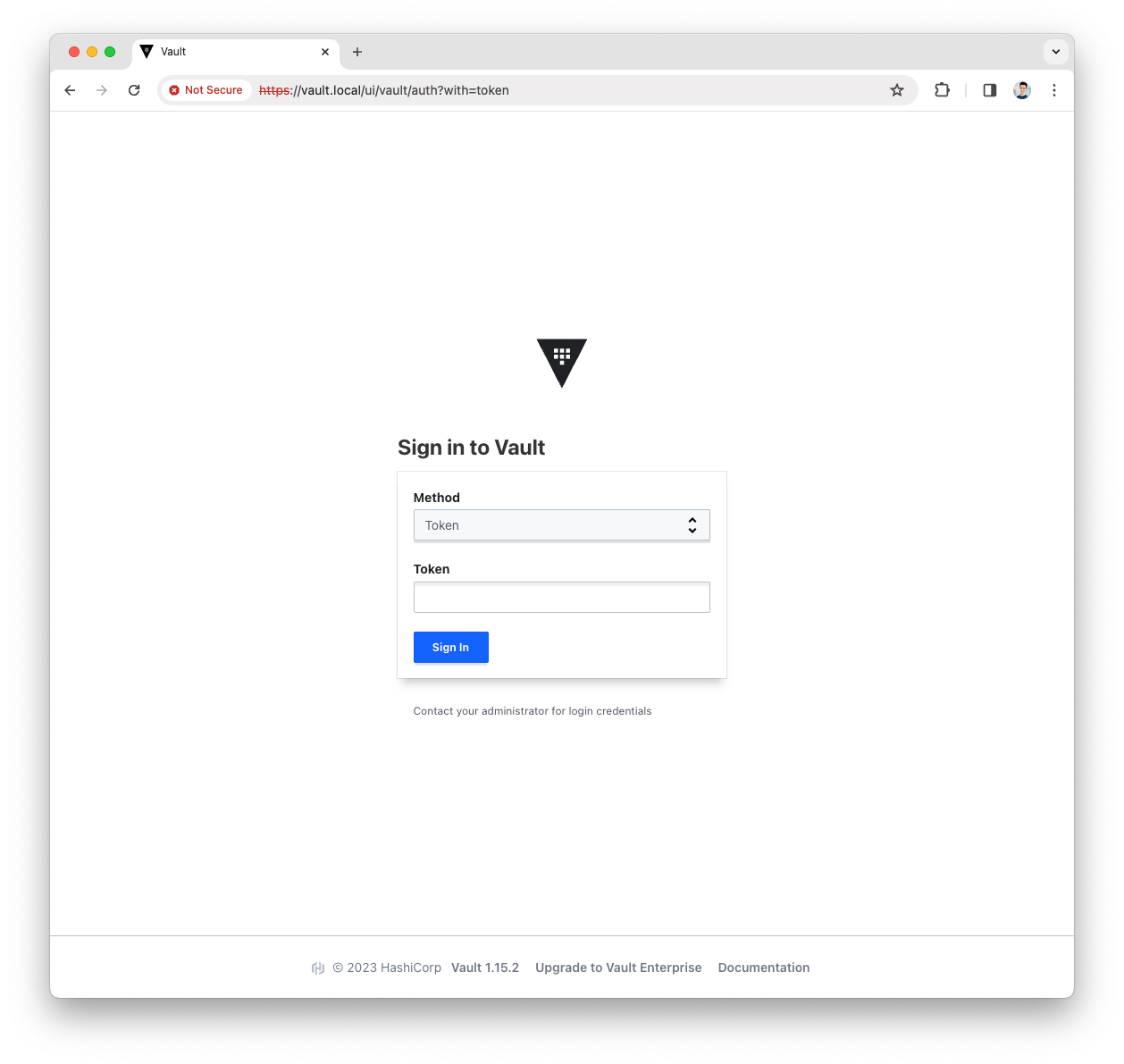
-
Open the
Accessmenu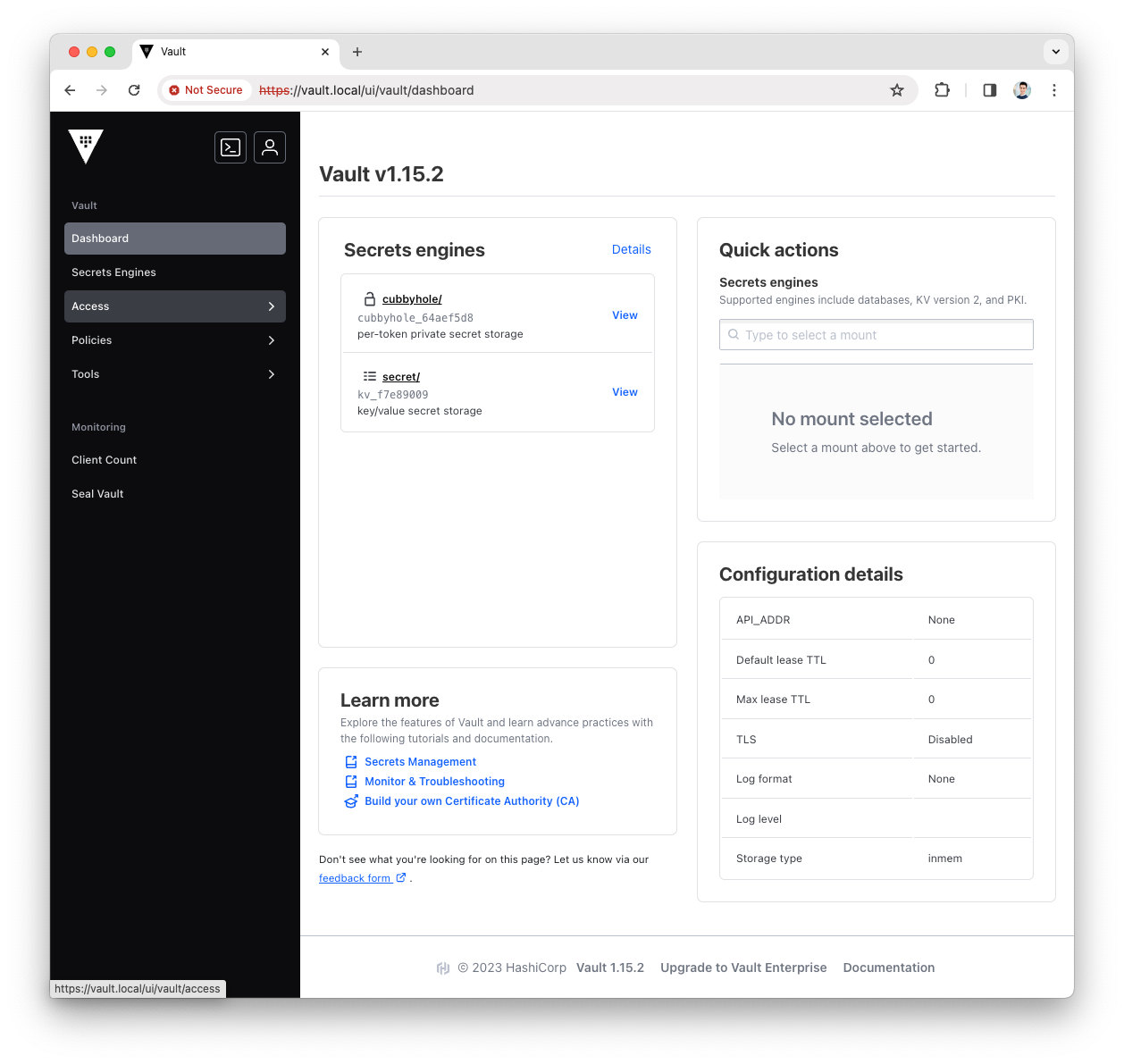
-
Press the
Enable auth methodbutton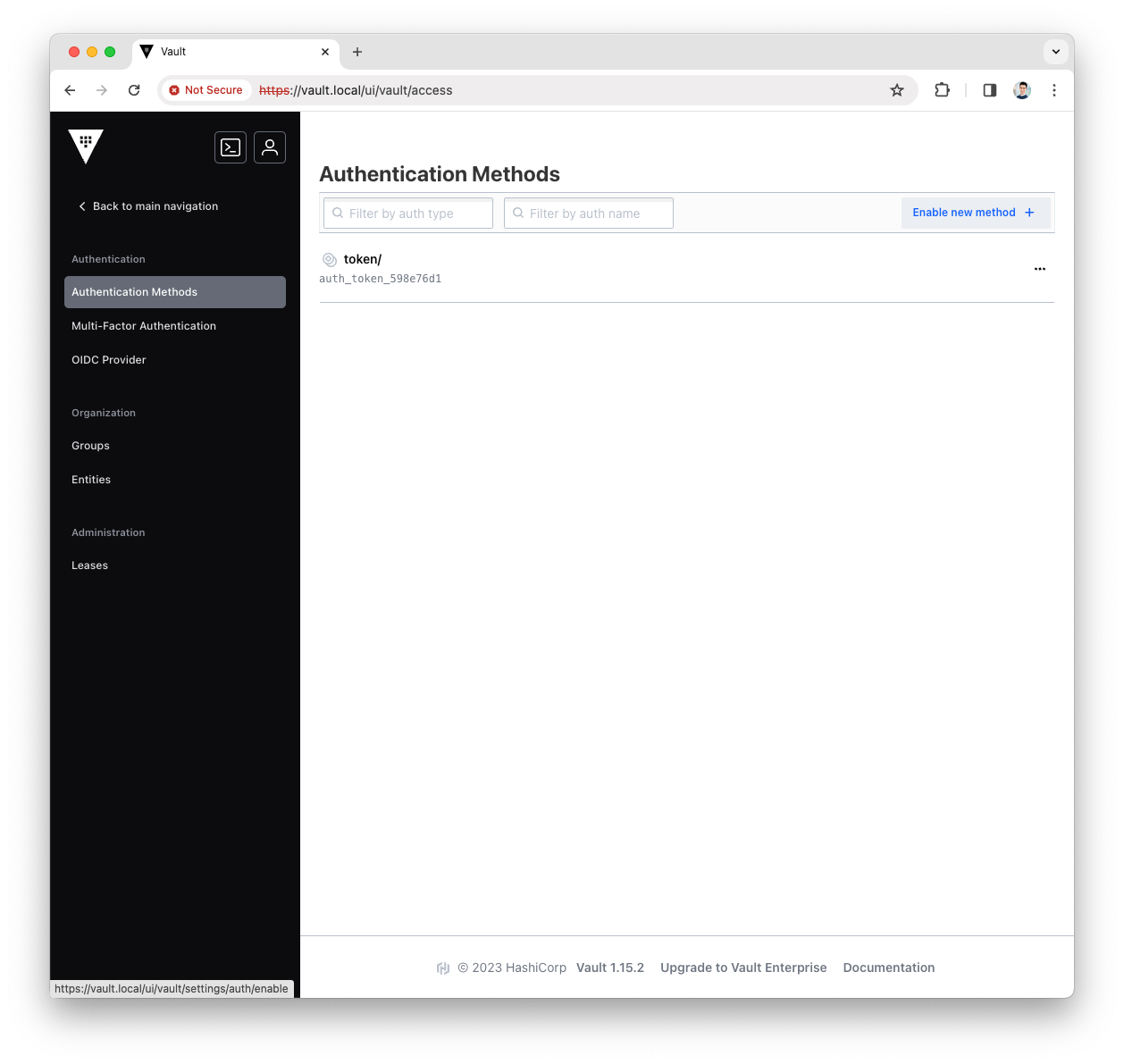
-
Select the
AppRoletype for the new Authentication Method and pressNext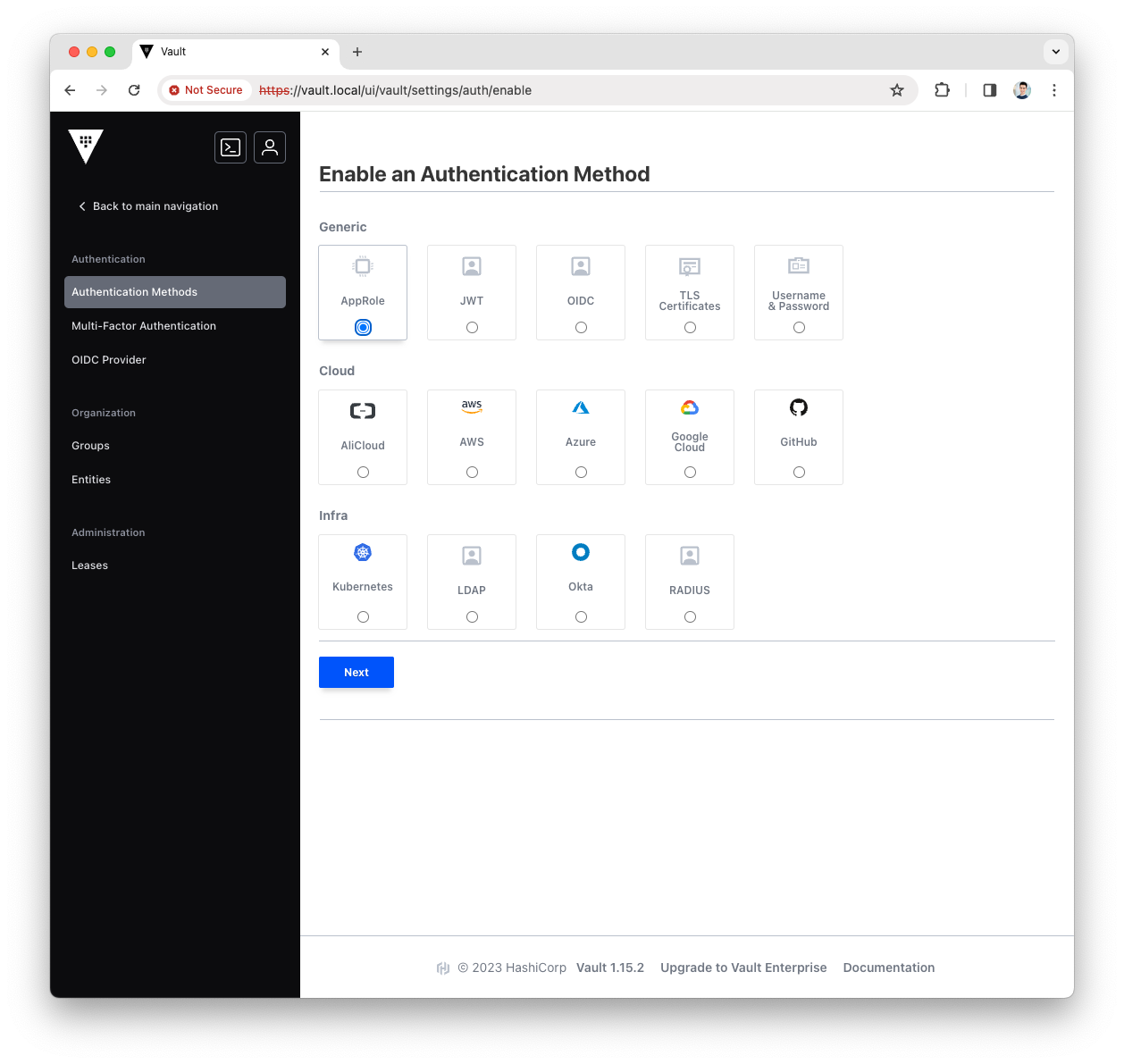
-
Fill the
Pathwith approle and press theEnable Methodbutton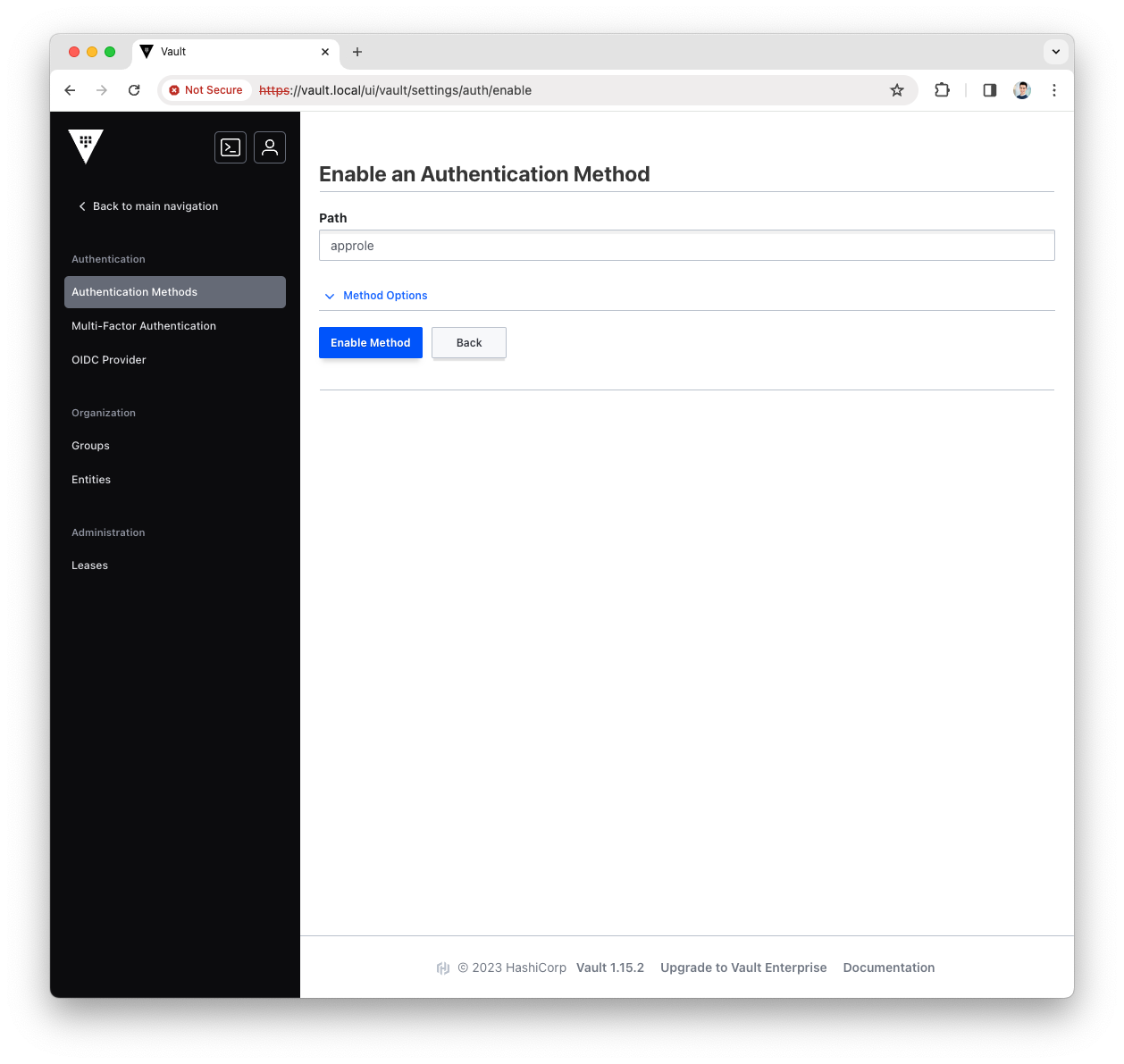
-
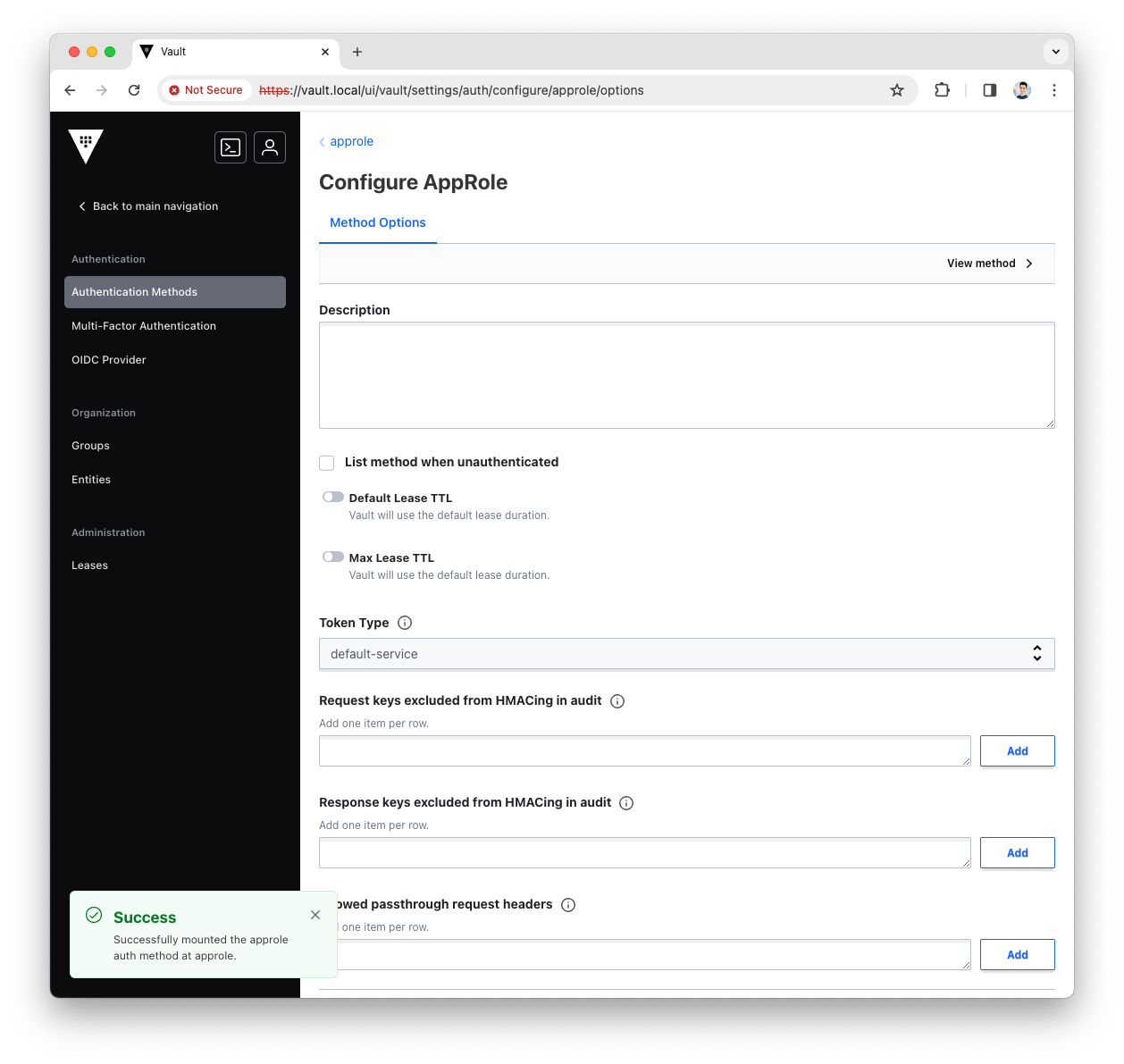
You have now enabled the AppRole authentication method, let’s use it with Platform Manager.
Create the KV Secrets Engine
The KV Secrets Engine is used to store secrets in Vault storage with Key:Value format.
More info can be found in the Vault official doc
-
Login into the Vault UI with the
rootToken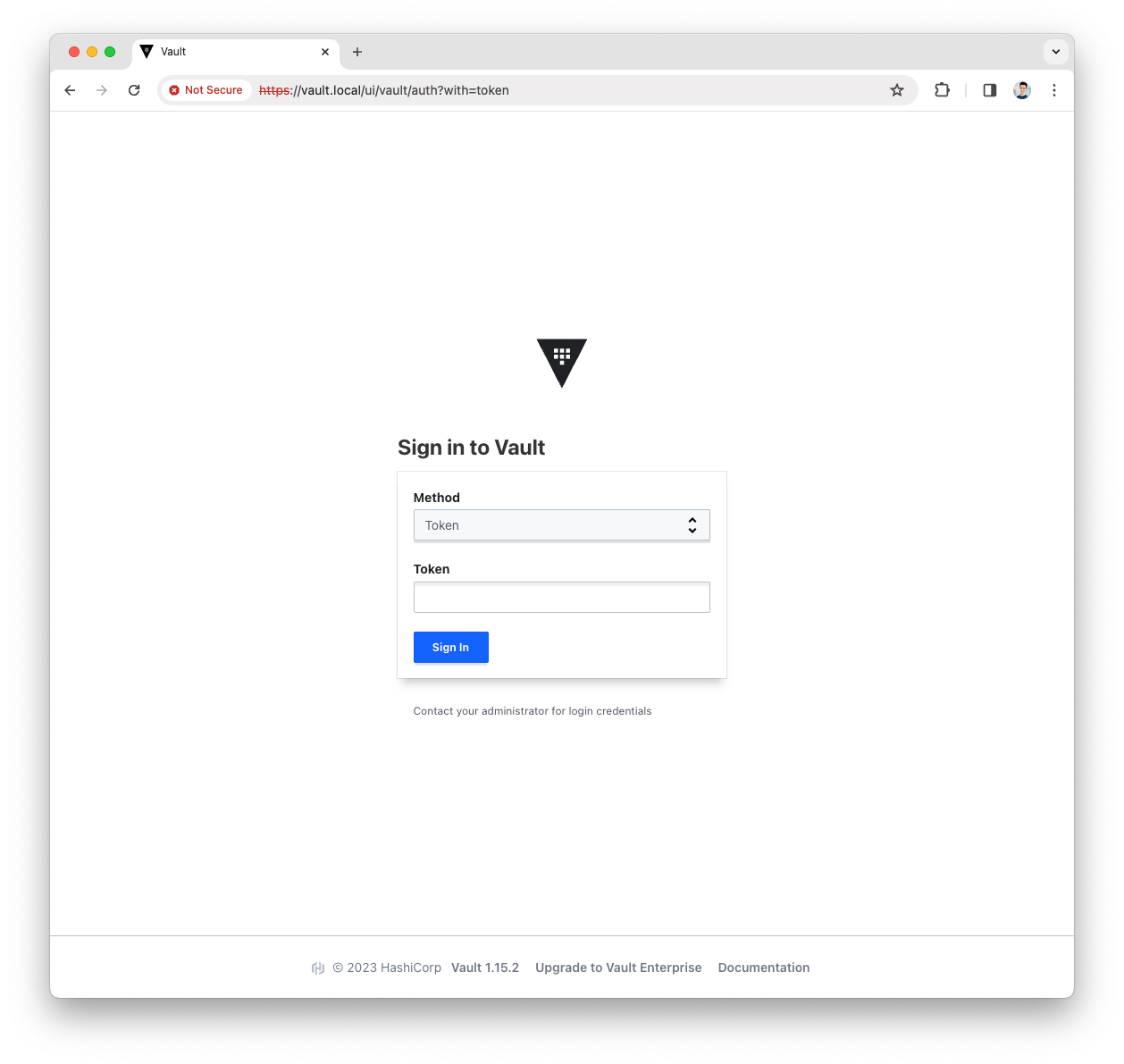
-
Open the
Secrets Enginesmenu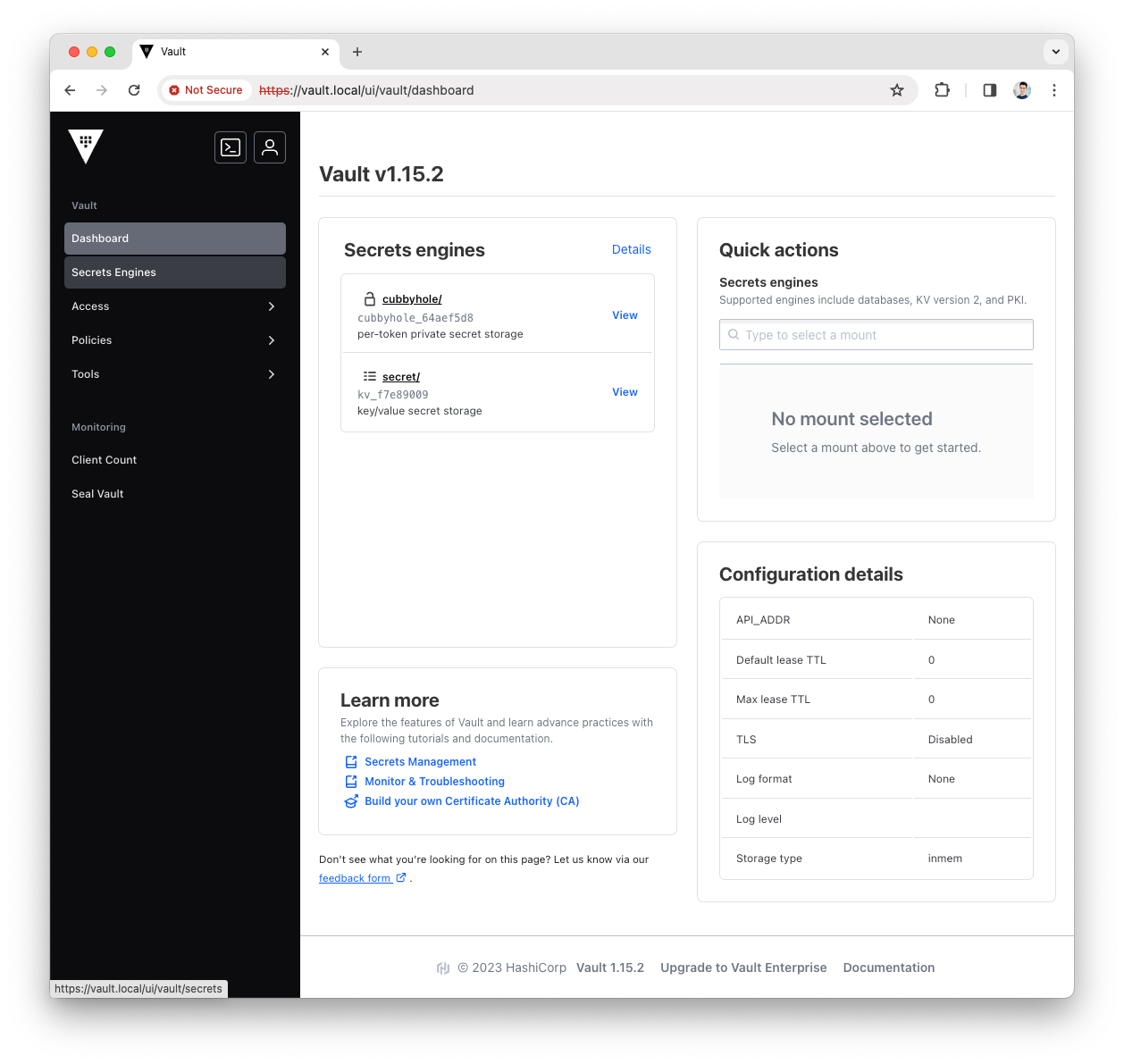
-
Press the
Enable new enginebutton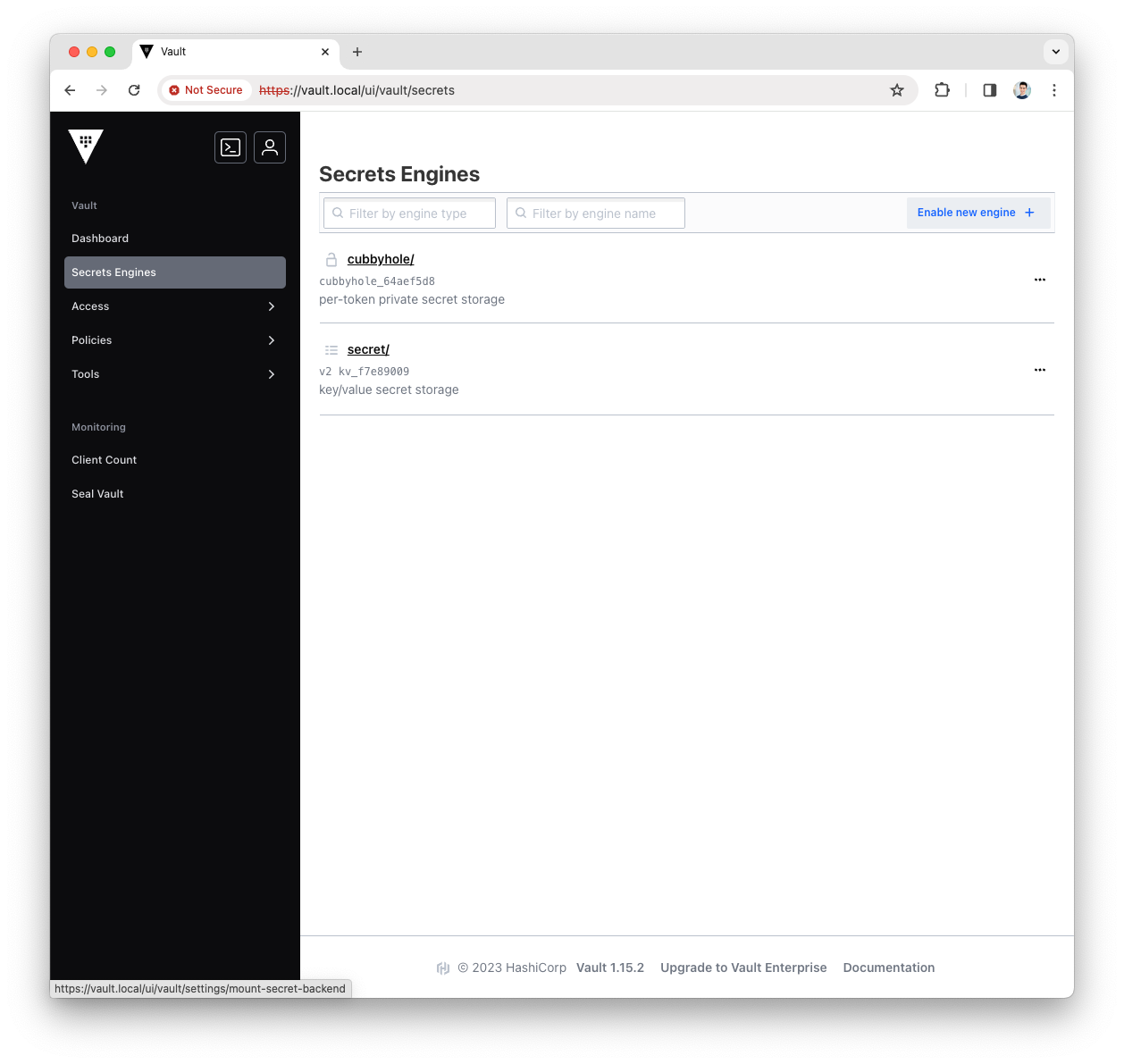
-
Select the
KVtype for the new engine and pressNext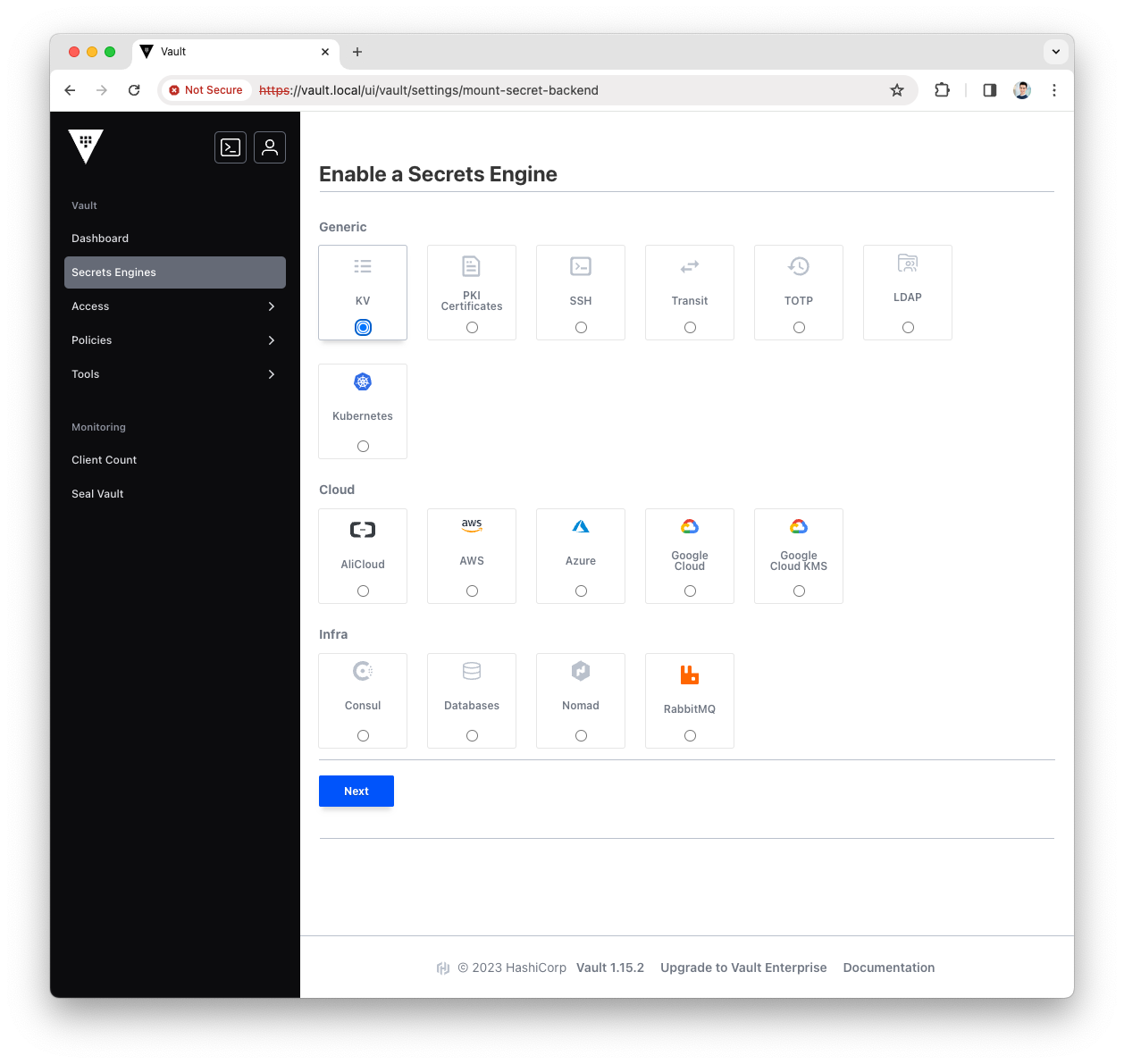
-
Fill the
Pathwith governance and pressEnable Engine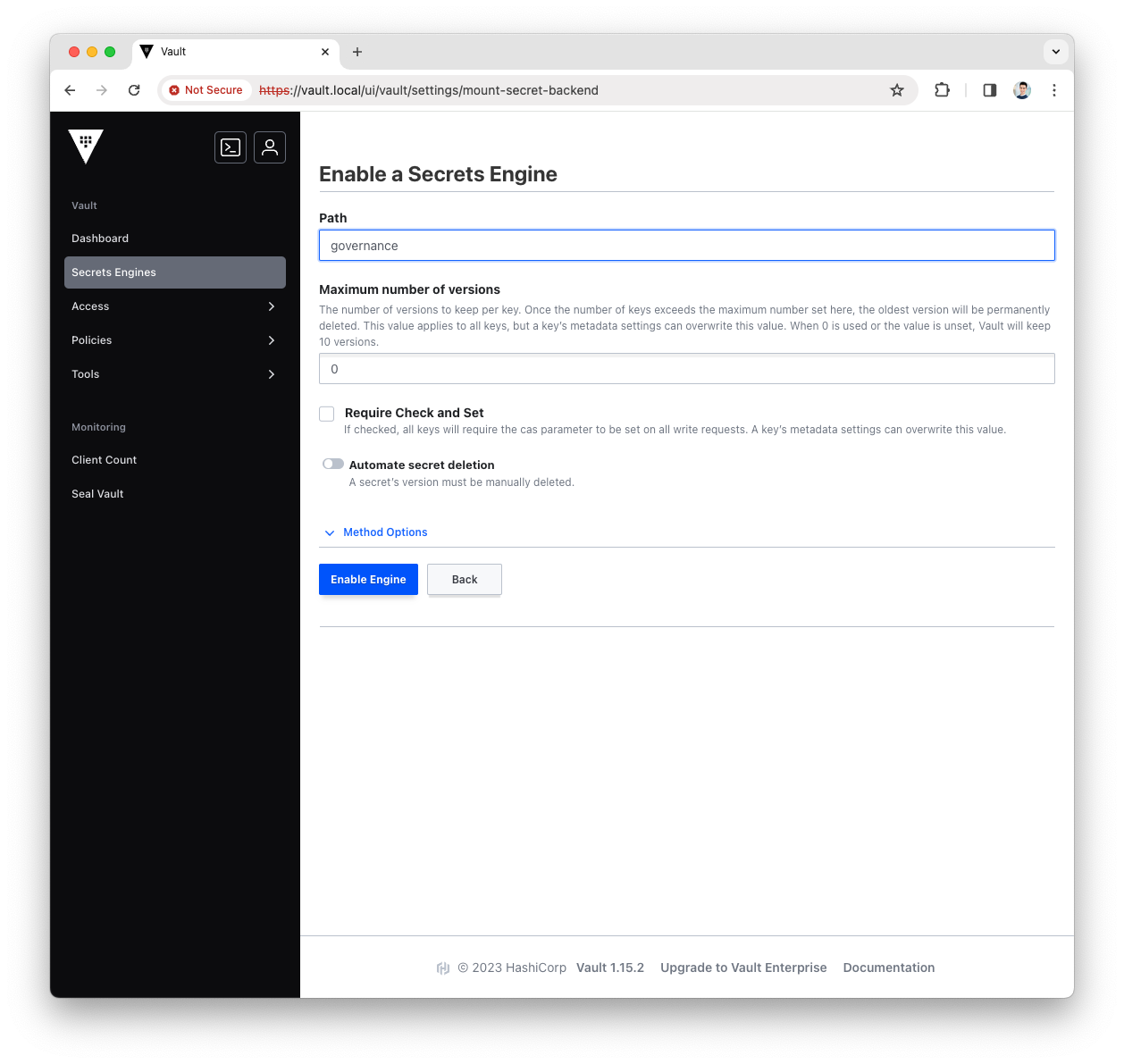
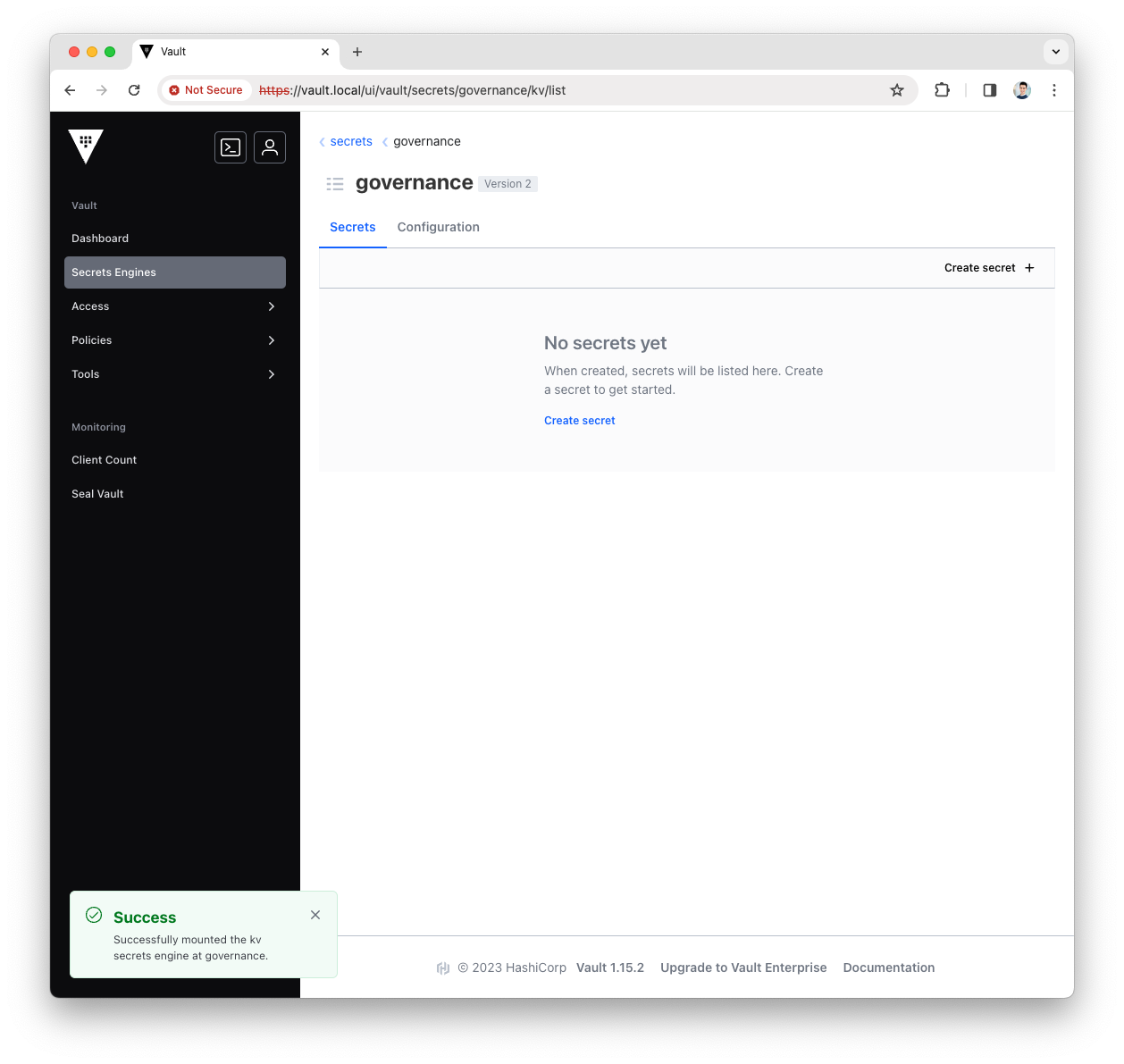
-
You have now configured the governance KV Secrets Engine, let’s use it with Platform Manager.
Create the Platform Manager Policy
Create the ACL Rule
The ACL Rule is a Vault Policy that provides a declarative way to grant access to a certain path.
More info can be found in the Vault official doc
-
Login into the Vault UI with the
rootToken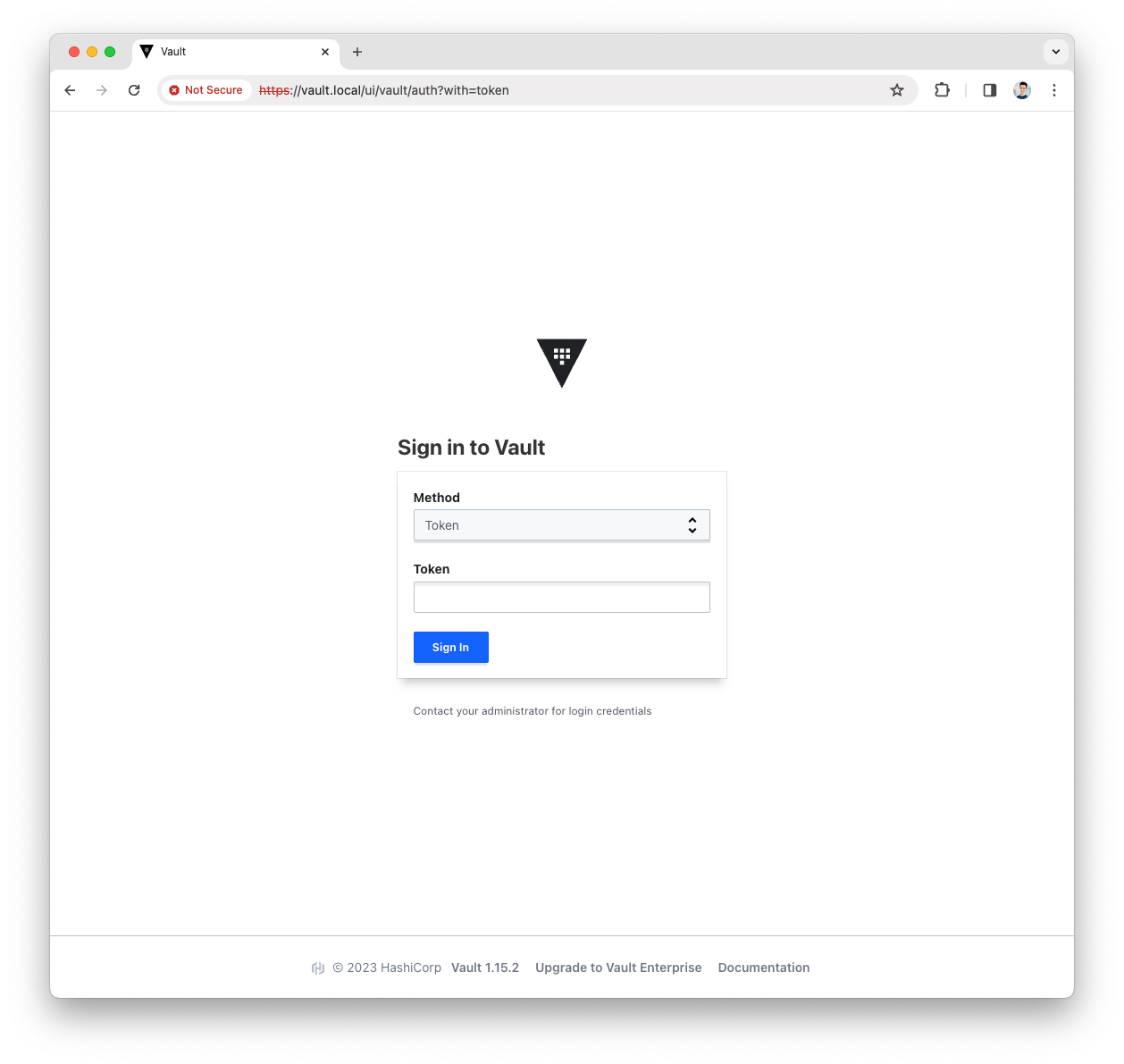
-
Open the
Policymenu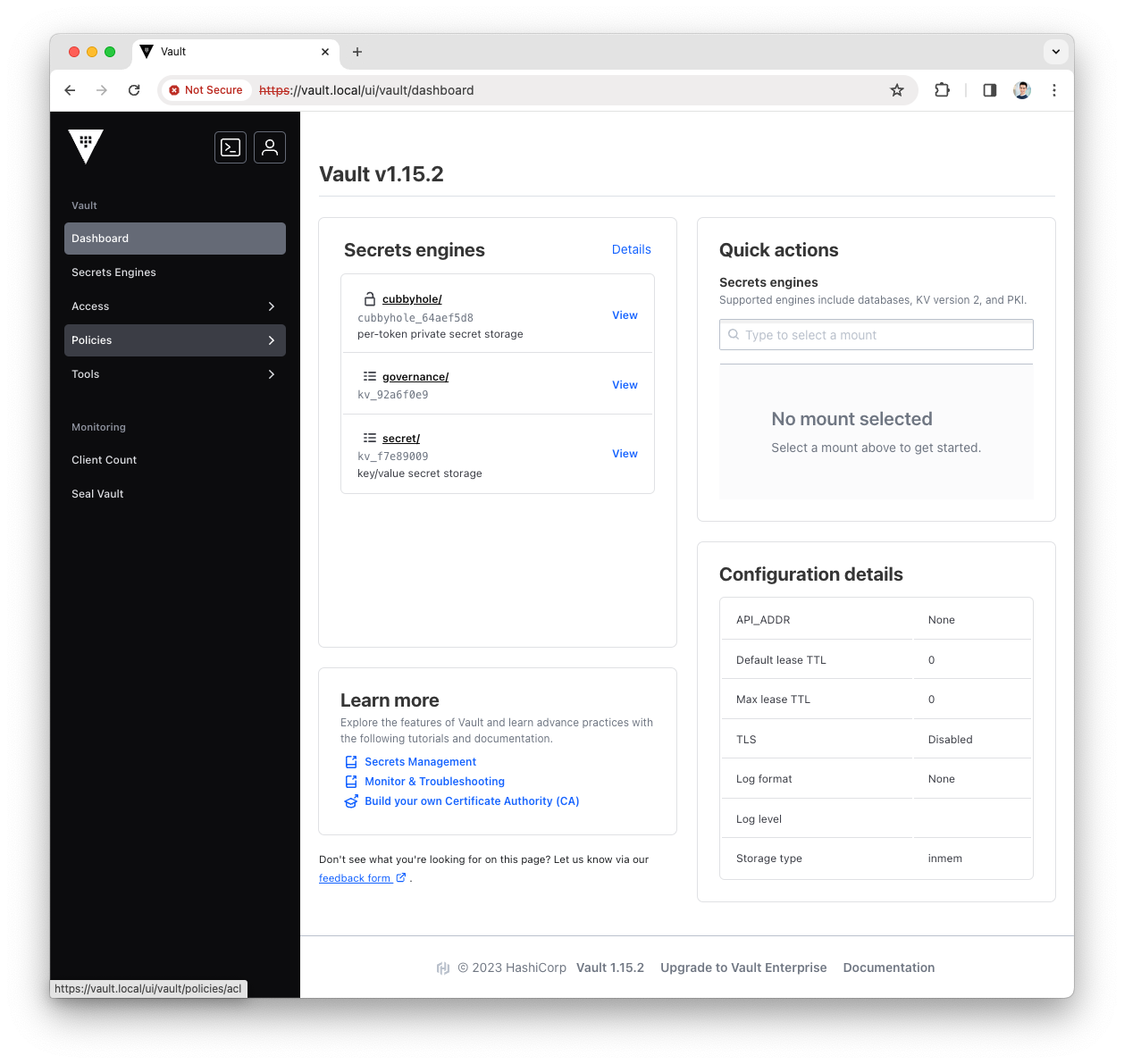
-
Press the
Create ACL policybutton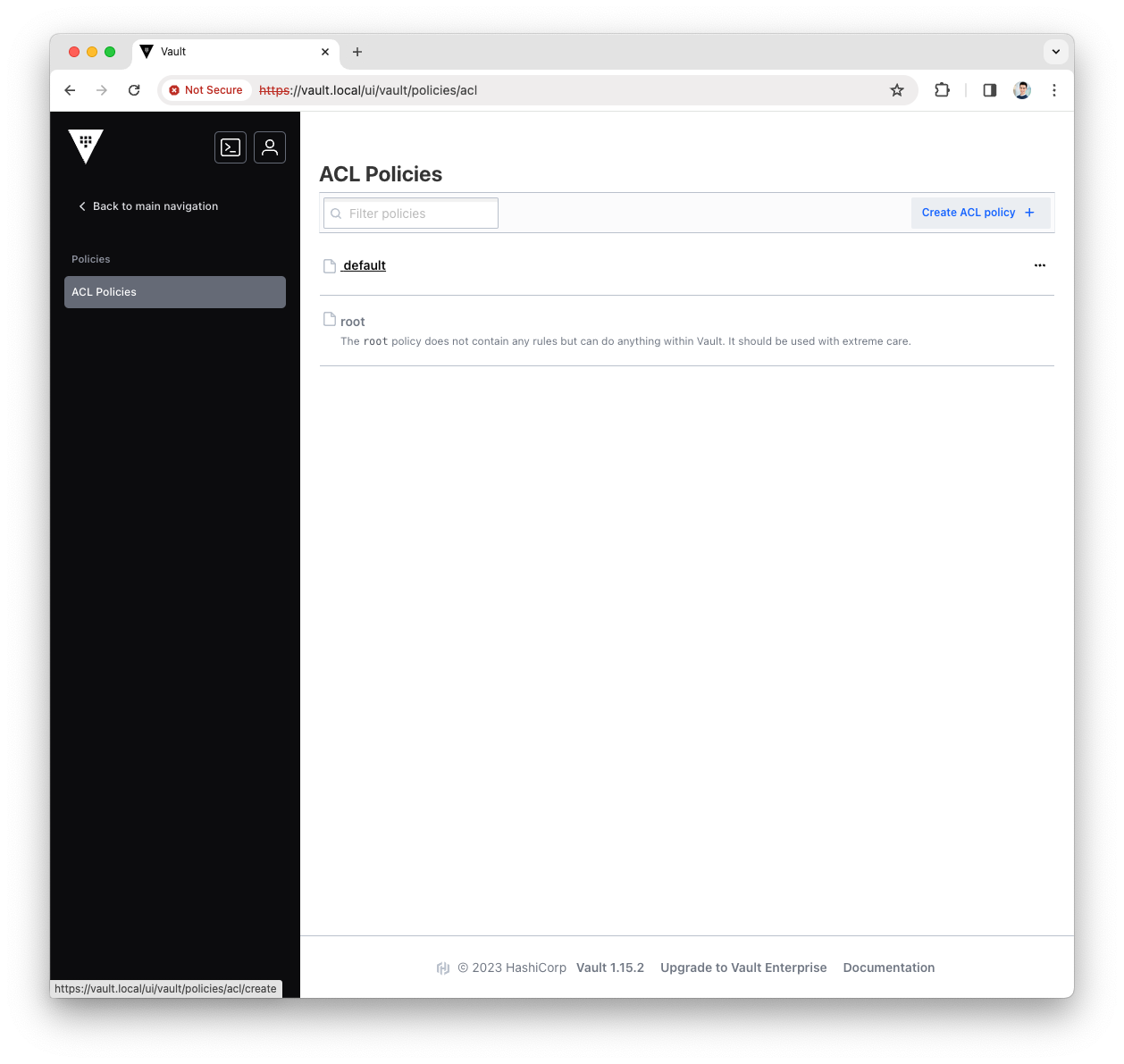
-
Fill the
Namewith platform-manager and copy the following content asPolicypath "governance/*" { capabilities = ["read","create","update","delete"] }
-
Press
Create Policy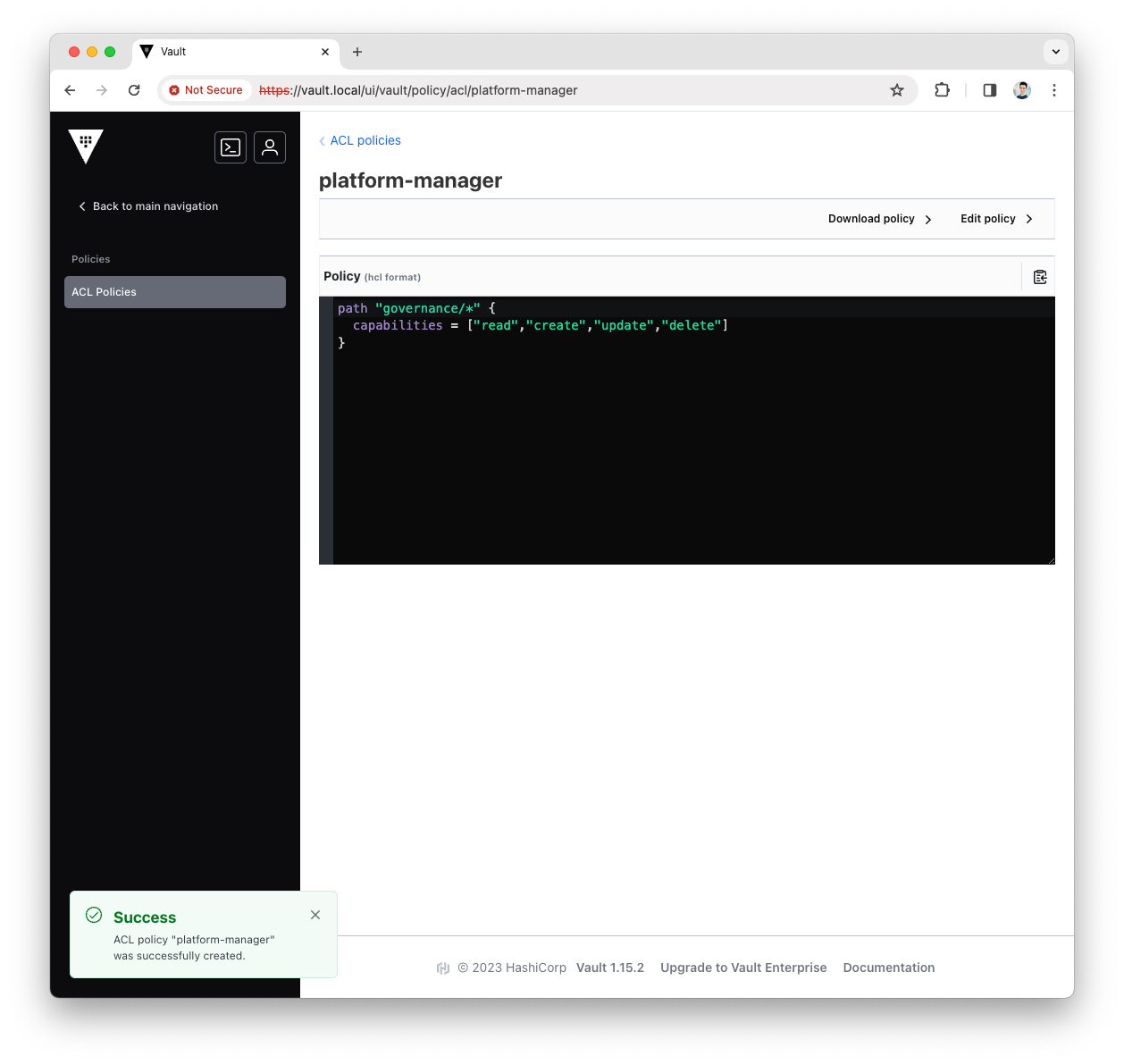
-
You have now created the Platform Manager policy, let’s add it to the Platform Manager AppRole.
Create RoleId and SecretId
-
Login into the Vault UI with the
rootToken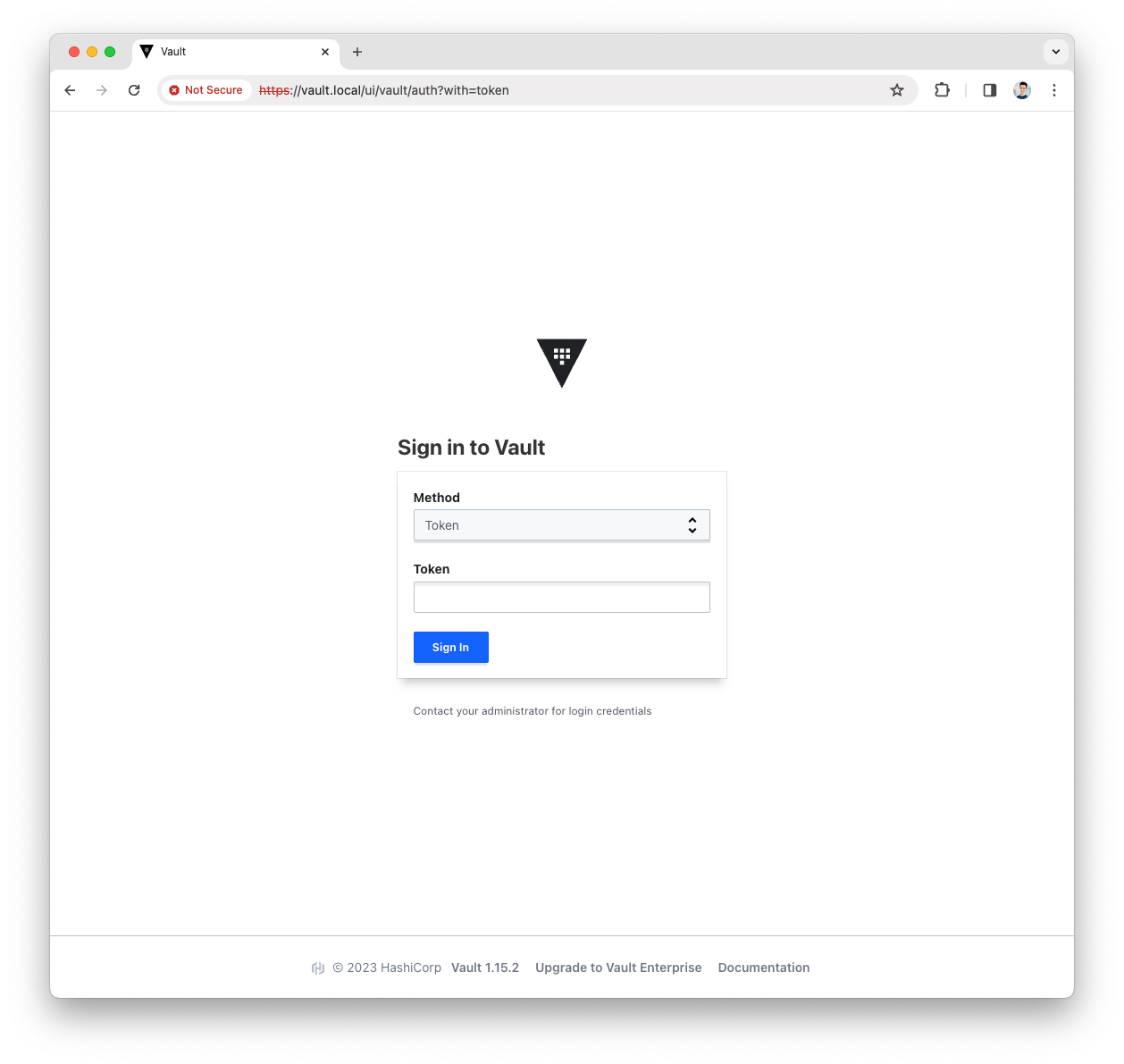
-
Open the
terminalmenu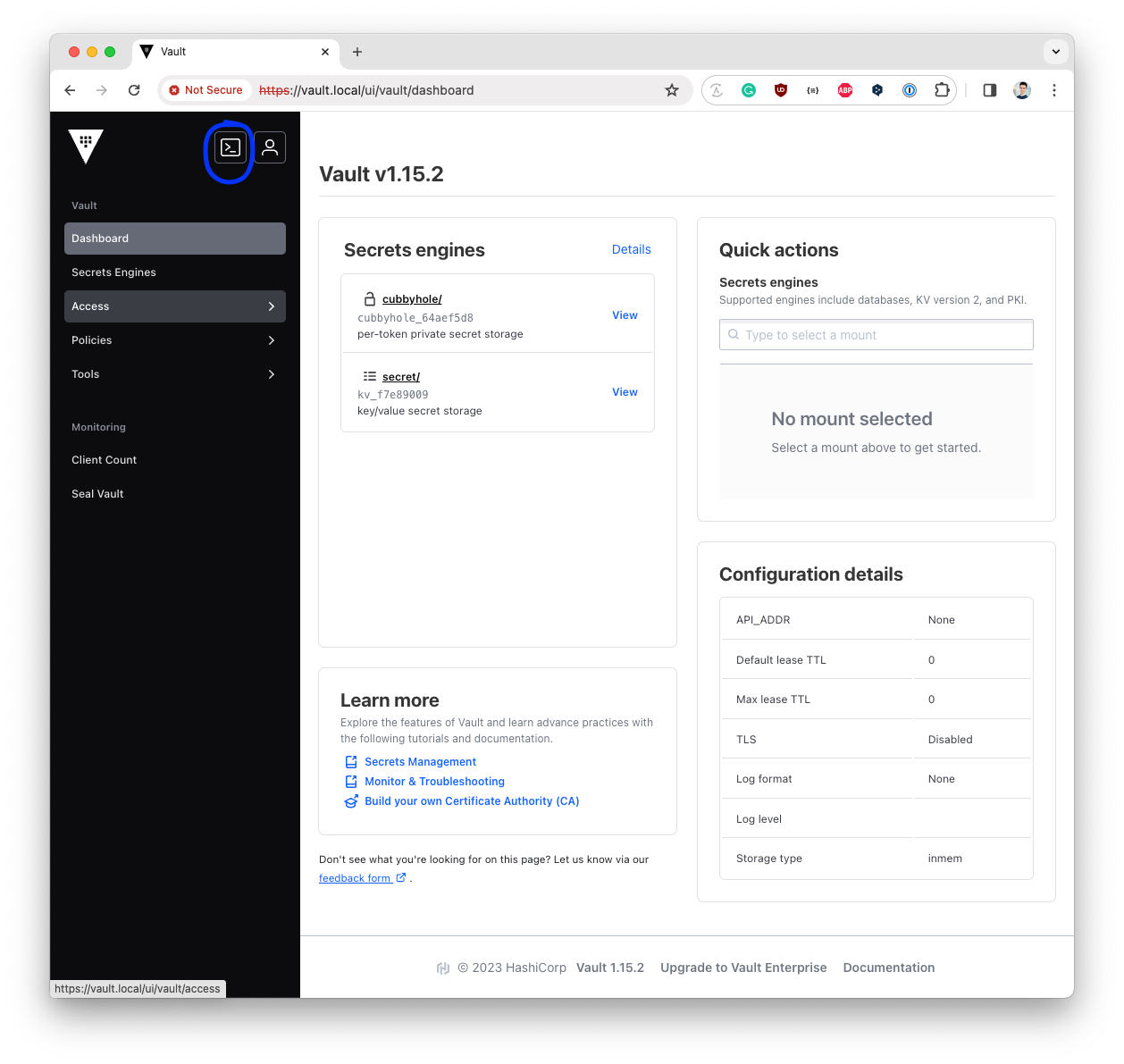
-
Add the Platform Manager policy to the
Platform Manager AppRolevault write auth/approle/role/platform-manager token_policies="platform-manager"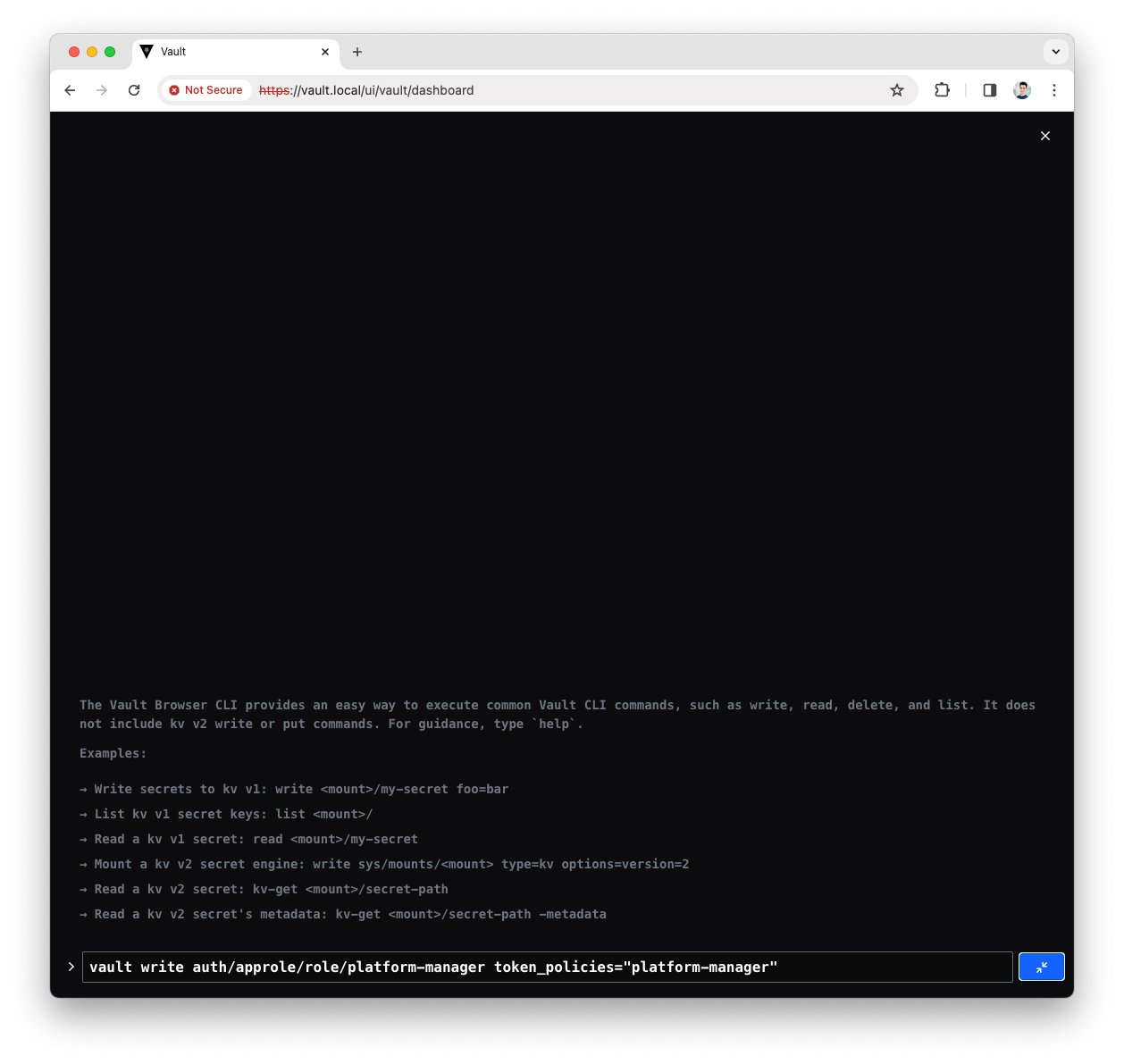
-
Read the Platform Manager policy
role_idvault read auth/approle/role/platform-manager/role-id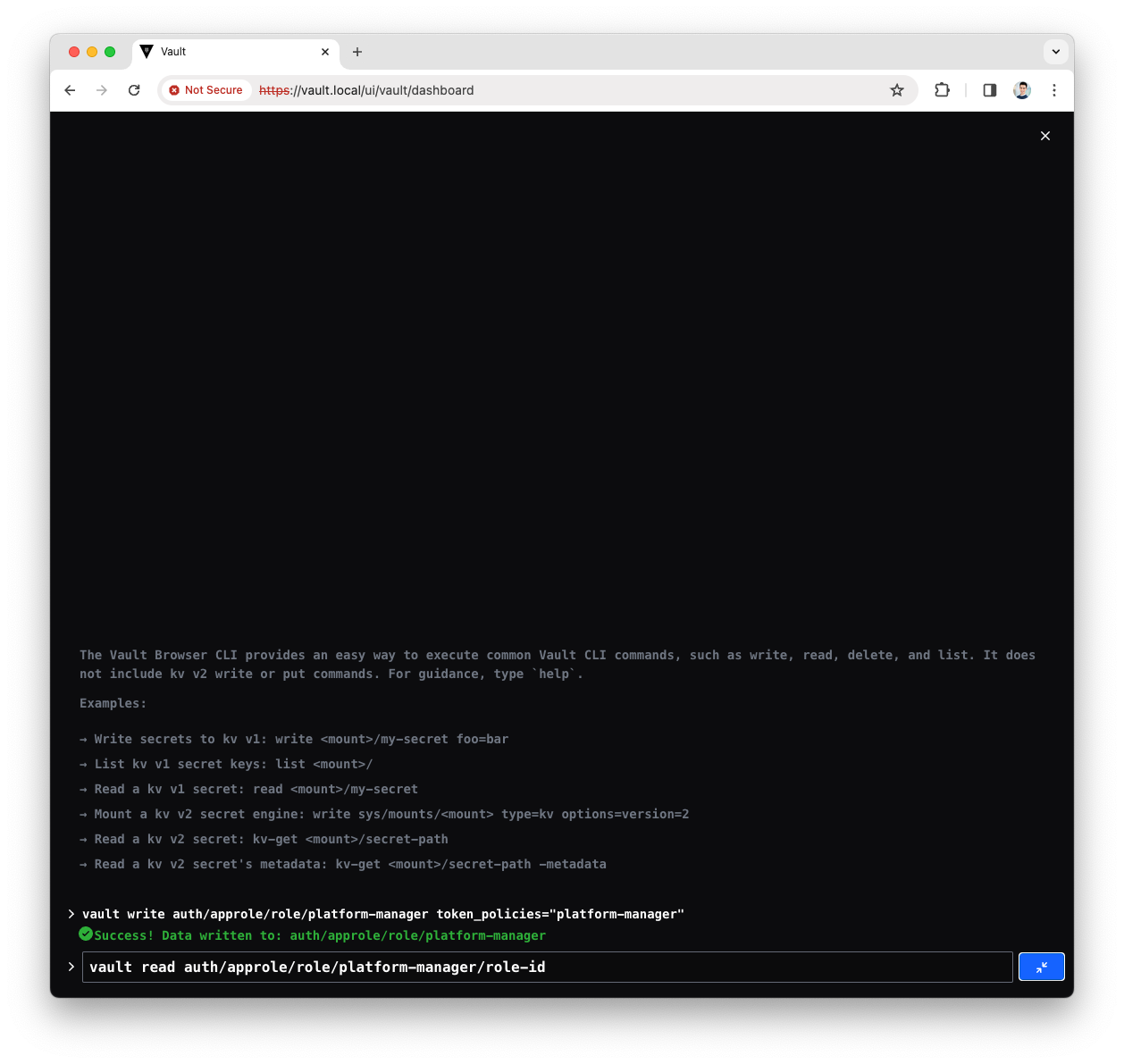
-
You will see a response like the following
Key Value role_id 0b7569bd-7d8b-c33c-f759-e15231b18542Note down the
role_id, will be used in the Platform Manager configuration -
Read the Platform Manager policy
secret_idvault write -f auth/approle/role/platform-manager/secret-id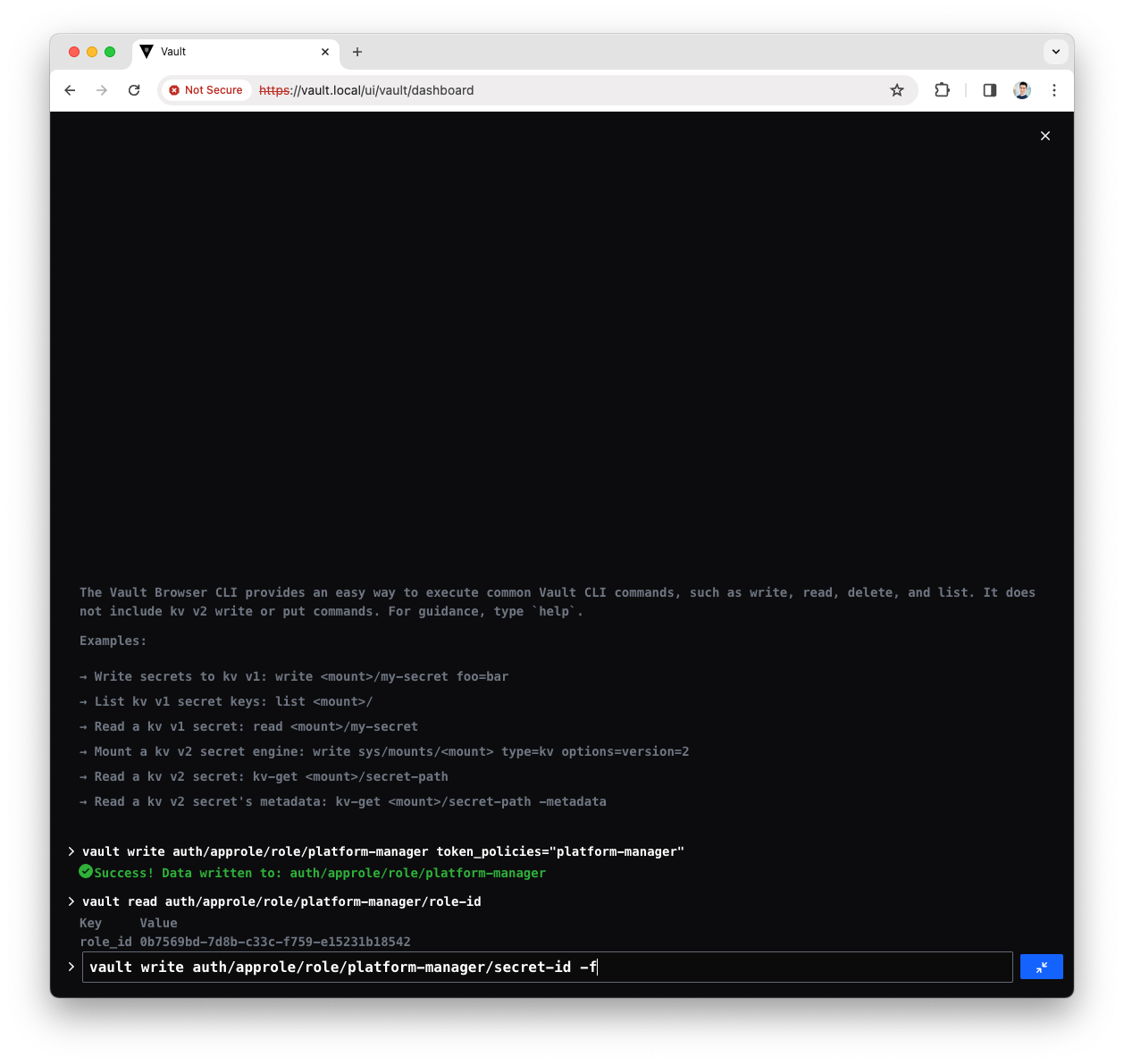
-
You will see a response like the following
Key Value secret_id 2387519d-5ac8-8af2-ad58-e89848fa3f05 secret_id_accessor a5740957-205d-7be4-23c7-e7bc57791631 secret_id_num_uses 0 secret_id_ttl 0Note down the
secret_id, will be used in the Platform Manager configuration -
Now you have done all steps to allow Platform Manager accessing the
governancepath.